SSH login to the bastion server
ssh -L 20202:XXXXXXXX:22 mickey.mouse@YYYYYYY -i C:\Users\t_yam\.ssh\aaaaaaa.pem-L
A signal that you should enter the address of the server you want to log in to.
20202:XXXXXXXX:22
states that the local port for the client on the local machine is to be forwarded to the specified host and port of the remote machine. In this case, local port 20202 on the local client is being forwarded to the same port (22) of the given remote server.
XXXXXXXX
IP address of the web server you want to ssh log in to via the bastion server. When operating multiple servers, enter the IP of the server you want to log in to.
mickey.mouse@YYYYYYY
The user name (mickey.mouse in this case) registered in the whitelist of the bastion server and the IP address of the bastion server.
-i identity_file
Full path to pem file and filename (aaaaaaa.pem in this case).
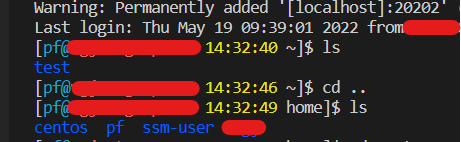
[mickey.mouse@disney-bastion-ec2 14:30:17 ~]$If something like the above is displayed, login is successful.
SSH login to the web server
Open a second terminal and enter the following command.
ssh pf@localhost -p 20202 -i C:\Users\t_yam.ssh\aaaaaaa.pem
pf is a user name that I have set myself in advance.
ssh pf@localhost -p 20202 -i C:\Users\t_yam\.ssh\aaaaaaa.pem
The authenticity of host '[localhost]:20202 ([::1]:20202)' can't be established.
ECDSA key fingerprint is SHA256:Ly8/CRMKoQZSVRZn/IFiIwyvFSN5uda2VRwzU.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yesType “yes”
If this is your first time connecting, you will be warned that “The authenticity of host ‘[localhost]:20202 ([::1]:20202)’ can’t be established.”.
At the same time, you will be asked if you want to continue connecting.
If you type yes here, the host information will be added to known_hosts and then authentication will proceed.
What is ECDSA Key fingerprint?
ECDSA key fingerprint is SHA256….: . Represents a key fingerprint using the ECDSA (Elliptic Curve Digital Signature Algorithm) encryption algorithm.
Warning: Permanently added '[localhost]:20202' (ECDSA) to the list of known hosts.
Last login: Thu May 19 09:39:01 2022 from aaa.aaa.aaa.aaaIf something like the following is displayed, login is successful.
What is Known-hosts?
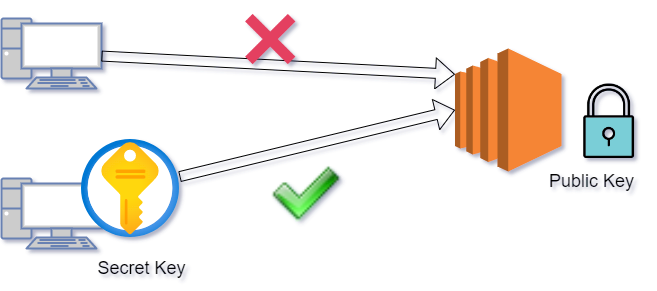
A text file that stores the public key of a host that has experience connecting.
If it is a user unit, it is located in .ssh / known_hosts.
Since the content is text, you can see it with cat etc.
It is enumerated by one host per line, and is a sequence of [host], address cipher suite public keys.
Some lines do not have [host].
Role of known_hosts
By registering in this file, by verifying whether there is a private key associated with the public key left at hand, it becomes a mechanism to notice even if the public key on the server side is changed.
On the SSH client side, even though the host has already connected even once, if a warning is issued, judge whether “the key has been changed” is unexpected.
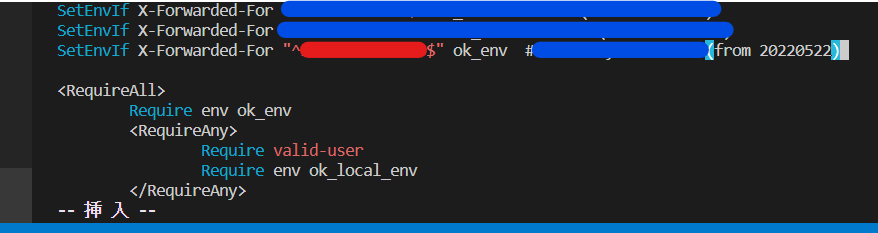
Manage connection with .ssh / config
config is a text file to be placed in the .ssh folder.
At least host information is required to connect to the SSH server with the ssh command.
-P option if SSH port is not the default 22
If you specify a user name, user_name @ before the host
-I option if the public key authentication key is not the default name
If you specify all of these, it will be long like below.
$ ssh pf@localhost -p 20202 -i C:\Users\t_yam\.ssh\aaaaaaa.pemFurthermore, if there are multiple connections instead of just one, it is a waste of time to enter the same information each time. By registering these in advance in config, options such as ssh command can be omitted.
For example, in the case of the SSH connection specified earlier, by adding the following settings to the config, only $ ssh disney is required.
Host disney
HostName YYYYYYYYY
User ec2-user
Port 2200
IdentityFile ~/.ssh\aaaaaaa.pemRecommend
EC2 with Security Group and SSH login